For many Mac users and IT professionals, a familiar cycle has unfolded over the years: an eagerly awaited macOS update, followed by the frustrating realization that once-reliable workflows have silently failed. Particularly troubling is the sudden breakdown of automation chains—AppleScripts, shell scripts, and Automator workflows—that are essential to daily operations. What’s often to blame? A permissions reset cascade that quietly wreaks havoc deep within macOS’s growing system security fabric.
TLDR (Too Long; Didn’t Read):
macOS updates frequently reset or reconfigure key system-level permissions, breaking previously functional automation workflows. This can affect scripting, folder access, and inter-app communication. Diagnosing and restoring permissions using a methodical “permission cascade reset” can often restore stability. This article explains why these issues happen and how users can systematically repair broken automation chains.
The Culprit: System Integrity Protection and TCC Evolution
Modern macOS versions, particularly since macOS Mojave (10.14), have introduced a layered approach to security. Through mechanisms like System Integrity Protection (SIP) and the Transparency, Consent, and Control (TCC) framework, Apple has hardened the operating system against privacy and malware threats. But this has come with unintended consequences—especially for power users and developers who rely on trusted automations to streamline their work.
Every update to macOS carries the potential to reset or invalidate prior approvals granted under the TCC framework. This might affect:
- Full Disk Access permissions required by automation tools.
- Automation permissions between applications (e.g., allowing Terminal or Keyboard Maestro to control Finder).
- Accessibility permissions for macro tools and screen readers.
In practice, your automation scripts relying on these privileges silently stop functioning. No clear system error presents itself, just a disconcerting silence where output was expected.
Symptoms of a Broken Automation Chain
Here are some of the most common signs that your automation chain has been broken after an update:
- AppleScripts that interact with multiple apps return cryptic “Not authorized to send Apple events” errors.
- Automator workflows stall unexpectedly without log output.
- Shell scripts lose access to protected directories like
~/Documents,~/Desktop, or external drives. - Third-party tools like Alfred, Keyboard Maestro, or Hazel stop performing expected operations.
If these symptoms coincide with a recent OS update, permissions are the likely culprit—not broken syntax or bugs in your automation logic.
The Permission Cascade Reset Strategy
To mitigate and resolve issues caused by TCC and SIP changes, we developed a method known internally as the Permission Cascade Reset strategy. This is a systematic, repeatable sequence of steps that will help you identify, diagnose, and resolve automation permission issues post-update.
Step 1: Identify All Apps Involved in the Chain
List every application and service in your automation, from scripting interfaces to file handlers or interface triggers. Each of them may require specific permissions that can be disrupted during an OS upgrade.
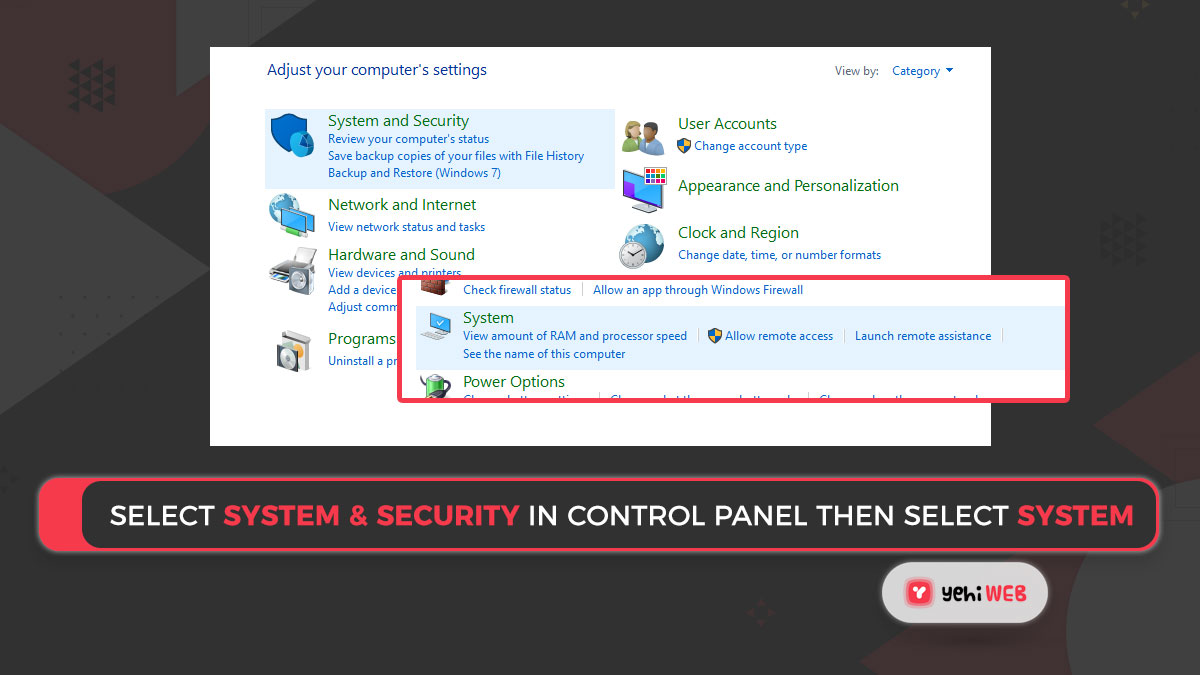
Step 2: Review System Settings for Missing Permissions
Navigate to System Settings > Privacy & Security, and check the following panels:
- Full Disk Access – Ensure all apps and automation utilities that need full file access are re-added.
- Accessibility – Tools that simulate keyboard or mouse input must be re-authorized.
- Automation – Key among these, this panel often drops prior inter-app automation approvals.
Pro tip: If your app appears grayed out or missing, remove it and manually re-add it via the “+” button.
Step 3: Use `tccutil` to Reset Permissions
Apple provides a terminal utility to reset TCC permissions. For instance, to reset permissions for a specific app:
tccutil reset All com.apple.TerminalAfter running this, re-launch the app and re-grant permissions as prompted. Be cautious: Use this only when you’re certain improper permissions are the cause.
Step 4: Reboot and Test in Isolation
After reassigning permissions, reboot your Mac. Why? Many security services and configuration files are only reloaded on startup. Then, run each component of your automation in isolation before restoring them into a chain. This will help you isolate issues like sandboxing restrictions or script-specific failures.
Real-World Case Study: Automation Failure at a Creative Studio
A mid-sized audio post-production studio relying on Folder Actions and AppleScripts experienced near-complete automation failure after updating to macOS Ventura. Audio file uploads were no longer triggering automatic sorting, and background tasks failed silently.
Tracing the issue, administrators found the following:
- The Folder Action scripts were no longer being triggered due to missing Automation permissions.
- Hazel lacked Full Disk Access and couldn’t monitor directories.
- Keyboard Maestro macros failed to simulate keystrokes due to missing Accessibility permissions.
By applying the Permission Cascade Reset strategy—identifying impacted app components, resetting tccutil entries, and rebuilding security trust relationships—they restored full automation workflow within 24 hours.

What Developers and Power Users Should Know
For consistent stability in automation post-update, it’s crucial to embrace the evolving principles of macOS security instead of working around them. Consider the following:
- Bundle Identifiers Matter: Automation permissions are associated with an app’s bundle ID. Cloned or rebuilt apps may require fresh authorization.
- Signed Scripts Preferred: Where possible, deploy signed AppleScripts and Automator actions. Unsigned scripts—even locally stored ones—face increased scrutiny under SIP.
- Keep Logs: Always log your automation scripts with timestamped outputs. Use `logger` or redirect script output to a log file so you can identify the moment something stops working.
- Automation Testing After Updates: Make automation testing a routine part of post-update checklists. Don’t rely on “set and forget” automation anymore.
Apple’s Quiet Evolution of Control
Ultimately, Apple’s software design philosophy prioritizes user privacy and system integrity over automation convenience. This requires power users to become more diligent and structured. While automation is still possible—even robust—it now entails a higher level of maintenance and authorization awareness than in pre-2018 macOS environments.
Final Thoughts
macOS automation breakage after system updates isn’t a bug—it’s an effect of increased protection layers introduced without automated migration for permissions. By understanding the permission cascade and using a repeatable methodology for validation and reset, users and admins alike can dramatically reduce post-update downtime and frustration.
In the age of increasing security hardening, the only automation that survives is the one that is monitored, tested, and maintained—just like the systems it runs.
yehiweb
Related posts
New Articles
Firebase Cheaper Alternatives for Startups and Developers
Firebase has become one of the most popular Backend-as-a-Service (BaaS) platforms for startups and independent developers. Its real-time database, authentication,…